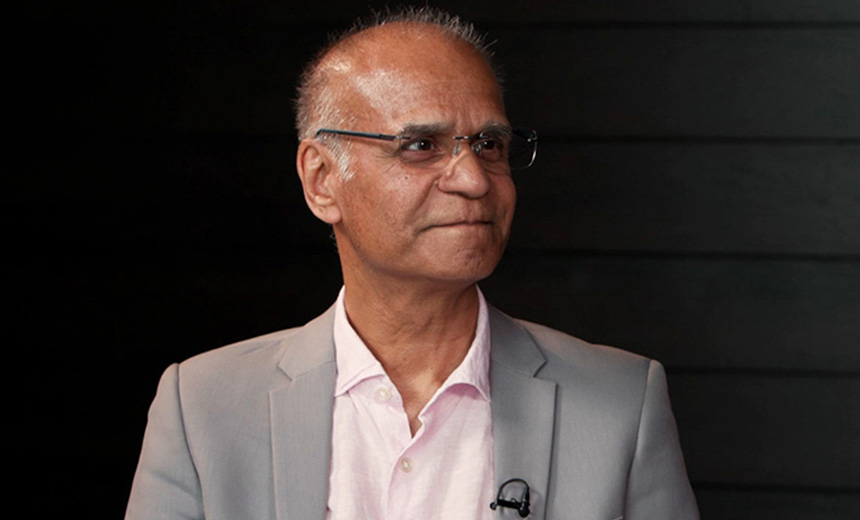
Sam Bankman-Fried, Fraud and the Future of Crypto
As the Sam Bankman-Fried courtroom saga continues, crypto policy expert Ari Redbord discusses the sentencing's impact of the FTX founder on the ecosystem and regulations, what lies ahead for the industry and approaches to curbing illicit finance threats in the space.